13Cyber security resume examples found
All examples are written by certified resume experts, and free for personal use. Copy any of the Cyber security resume examples to your own resume, or use one of our free downloadable Word templates. We recommend using these Cyber security resume examples as inspiration only, while creating your own resume.
Learn more about: how to write a perfect resume
Demonstrated ability to work on multiple tasks and respond to rapidly changing priorities under the direction of the IT Manager. Formulated, organized, and effectively presented ideas while serving as the company’s official representative in technical forums and panel discussions.
Developed, installed, and monitored security software and hardware components for the company’s network. Assisted with the configuration and optimization of IT tools, and performed vulnerability scans, web applications, penetration tests, and security assessments.
Provided the highest level of technical expertise in the analysis, installation, configuration, testing, and maintenance of Enterprise Technology Architecture. Supported all phases of projects, programs, and initiatives to facilitate requirement elicitation for application servers and content management.
Responsible for managing firewalls and network security components and devices to provide timely, accurate, and planned completion and implementation of security services for the organization. Supported clients with data protection, the internet of things, and overarching cloud capabilities.
Managed a $10M budget to operate and defend 3 unique networks for client engagement in accordance with SOW, exceeding KPIs. Supported 1K users; overseeing 10 direct reports including 4 division managers executing vulnerability management, cyber protection, incident response, and cyber forensics analysis as well as protection management, cyber intelligence, and reporting. Rebuild client trust and course‐corrected program after winning mismanaged contract.
Developed technology roadmaps for security tools in alignment with the company’s business objectives while partnering with the executive team and cross-functional global teams. Functioned as a key strategic member of the Security Steering Committee and Security Governance team. Supervised 7 direct reports. Managed up to $30M in project budgets and $5M in IT P&L.
Directed a broad range of IT initiatives for a diversified education and media company. Provided incident/situation management and ongoing technical training to over 500 users while resolving issues promptly with ITIL methodologies. Supported over 130 licensed users annually.
Implemented core and cloud infrastructure security systems to identify and manage network risks. Led network architecture and operational complex network solutions to rapidly changing technologies and complex company environments. Trained and led network technologists to deploy complex solutions.
Conducted regular surveys and audits of cyber security programs and provided assistance and consulting services to all departments. Oversaw firewall, email security systems, web security systems, and IDS/IPS. Maintained a current understanding of all applicable DOE and Federal regulatory requirements.
Worked cross-functionally with our software and hardware development teams to ensure security threats are identified, prioritized, and resolved promptly. Contributed to the development and implementation of security policies and procedures to support confidentiality and integrity.

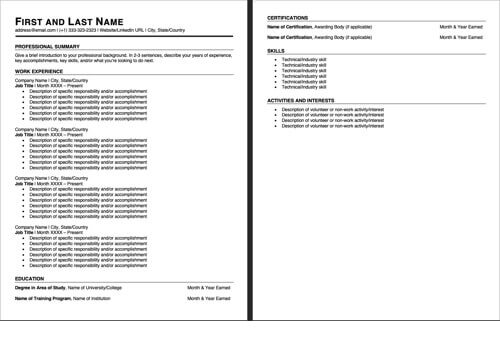
Make a resume that wins you interviews! Choose one of these professionally-designed resume templates and follow 3 easy steps to complete.
Create a perfect resume in a few minutes

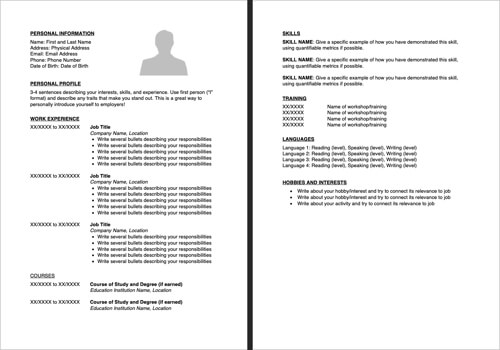
Download our American style resume template. Chronological resume format. Download a functional resume template.
Learn more about the differences between a resume and a CV.
Download our British/European style cv template. Similar to a resume but more commonly used in Europe, Asia and Africa.